At the end of February 2020, I reviewed top-level takeaways from Revenera’s 2020 State of Open Source License Compliance Report. Taking a closer look at the report’s findings, I blogged about how vigilance about open source risk can help software businesses be agile and addressed how to prioritize and work through risks. Stay up to date with our posts by clicking the “subscribe” link at the top of this page.
When I’m asked about what level of software audit analysis is most appropriate for a company, I frequently respond with, “How much risk are you willing to assume?”
There are times when a detailed open source scan is absolutely necessary. At other times, an overview may be appropriate and sufficient.
Let’s take a look at the types of audits Revenera conducts, how deep – or not—scans go, what they find, how they can meet the changing requirements of your business, and why each plays an important role in securing your use of open source software.
Audits as Part of the SCA Process
Software Composition Analysis (SCA) is the process of automating the visibility into open source software (OSS) use for the purpose of risk management, security, and license compliance. With the rise of open source (OS) use in software across all industries, the need to track components increases exponentially to protect companies from issues and open source vulnerabilities. Because the majority of software creation includes OS, manual tracking is difficult, requiring the need to use automation to scan open source software code, binaries, and dependencies.
Open source audits do the work of discovering open source. Audits provide an analysis of third-party and proprietary software, allowing you to fully understand open source license compliance and vulnerability issues. Audits produce a software bill of materials (BOM) for updating and remediation.
What Do Audits Evaluate? 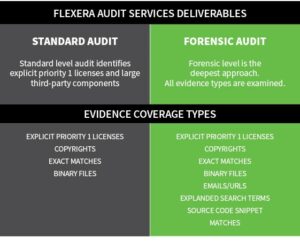
The 2020 State of Open Source License Compliance Report included three types of audit services: standard, forensic, and targeted. Targeted audits are customized and are designed to meet aggressive timelines, budgetary needs, or to target specific areas of the codebase. Here we’ll look at the two more frequently discussed types of audits: standard and forensic.
- Standard Audit services are most commonly requested when your team needs to vet code from an external supplier; when you need supporting materials for IP litigation efforts; when your organization is releasing a software project or solution under an open source license; and when you’re about to reach a development milestone and need to ensure both compliance and security before the release. Our experienced auditors know how to point out files that will be open source, including the large, very apparent third-party open source items, such as a file called “Open SSL.”
- The codebase scans identify explicit P1 licenses (discussed in my last post) and significantly large third-party components with a concentration on copyleft licenses, such as the GNU General Public License. Evidence types include most (but not all) explicit P1 licenses, copyrights, exact matches, and binary files.
- Forensic Audit services provide a deeper analysis. Why might your organization need to go to the effort of this more detailed review? Perhaps the cost of accidental infringement would be too high and extra caution upfront is warranted to offset potential costly litigation or loss of reputation down the road. Another common reason is when circumstances suggest that normal signs of third-party use—such as copyrights or license text—may have been removed. Some companies do not want to take on any risk at all and will always do forensic (rather than standard) audits.
- Forensic audits provide in-depth, deep level scan examinations of all evidence types, including explicit P1 licenses, copyrights, exact matches, binary files, emails/URLs, expanded search terms, and source code snippet matches and fingerprint analysis to identify copy and pastes of source code. These look not just at the file level, but at each line of code and take a deeper look at the non-explicit evidence, reviewing items that don’t have notices identifying them as third-party code. Forensic Audits discover 6% more issues per project than do standard audits.
The choice of audit type depends on company policy, business needs (such as an M&A event), market fluctuations, size and type of codebase, and threat actors. Managing the risk doesn’t just fall to the developers, but to a full team representing engineering, legal, leadership, and the Open Source Review Board (OSRB), as well.
For more information about Revenera Open Source Software Audit Services, download our datasheet.



